In my previous Trend Micro blogs , I have explained about the Trend DSM and the Relay Server Installation and in this blog we can see the installation of vSheild Endpoint and its configuration with Trend and the ESX host.
vShield Manager:
vSheild Endpoint is free with ESXi STD , ENT and ENT + and it is one of the function of the vSheild Manager and I believe if we have the license for vCenter and ESXi then we can able to download the vSheild Manager also.
vSheild Manager needs to be deployed in order to install the VMware vShield Endpoint APIs with Trend will provide agentless anti-malware protection for VMware virtual machines with zero in-guest footprint. Helps avoid security brown-outs commonly seen in full system scans and pattern updates .
Pic was taken from the Trend Doc.
vShield Endoint:
Pic was taken from the VMware , Pls refer the below reference link for more info about the vShield Endpoint.
vShield Endpoint Installation:
After Login to the vSheild Manager, Select the host and go to summary in which we can see the vSheild EndPoint Service and its status and Click Install.
After the installation , we can check the vShield Endpoint driver running on the ESX host by the command.
ps | grep vShield-Endpoint-Mux
By using the esxcfg-advcfg –get /UserVars/VshieldEndpointSolutionsConfiguration command we can check the configuration of the vShield Endpoint with the DSVA ( Pls see the DSVA section for more info)
Once the Installation is done, we need to make sure the installation is configured correctly by checking the Networking Settings on the ESXi , there will be a new standard vSwitch was created. This will be an internal vSwitch ( vmservice-vswitch ) with no adapters and the filter drivers on the ESX host will redirect all traffic via the internal switch.
Following Port Groups will be available under the vmservice-vswitch
- vmservice-vshield-pg
- vmservice-vmknic-pg
- vmservice-trend-pg – This port group will be added only after the Trend Filter driver installtion on the host.
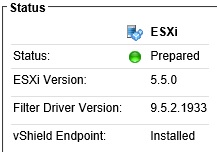
From the DSM Console also we can check the vSheild Endpoint status.
vSheild Endpoint configuration with VMware tools.
After the Installation of vSheild Endpoint on the ESXi hosts , we have to install the VMCI driver. It will be part of the VMware Tools and embedded as the vSheild Endpoint driver. By default it will be in disable status and we need to enable the same by modifying the features installed in VMware tools. Select the vSheild Endpoint driver from the list of features and install on local hard-drive.Once we enable the drivers then realtime malware protection will be available.Pls note the below is for only the windows server and for unix\Linux we need to install the agent from the trend .
Pls check my VMtools blog for more information.
Also use fltmc command to check the vsheild driver ( vsepflt )is running or not and also use load and unload command to enable and disable the driver.
fltmc unload\load vsepflt
To monitor the vSheild Manager , check the link which explains the steps.
In my next blog we can see the installation of Trend Filter Driver and its function .
Reference : I would recommend to read the below link from VMware which explains about the vShield end point features and functions.












Pingback: Trend Micro Deep Security 9.5 (Relay Server) -Part 2 | Techbrainblog
Pingback: Trend Micro Deep Security 9.5 ( Filter Driver Installation ) – Part 4 | Techbrainblog
Pingback: Trend Micro Deep Security 9.5 ( Deep Security Virtual Appliance-DSVA) – Part 4 | Techbrainblog
Pingback: Trend Micro Deep Security 9.5 ( Deep Security Agent ) – Part 6 | Techbrainblog
Pingback: Trend Micro Deep Security 9.5 ( Smart Scanning Protection Server – SSP Server) – Part 7 | Techbrainblog
thnx for this
LikeLike
Pls check my other Trend blogs also and will post few other topics on trend soon …..
LikeLike