In this Blog I will explain the features and the functionality of the Trend Deep Security product. Trend Micro Deep Security has few components which will provide protection against Malware in real-time, Intrusion prevention. Web Reputation, Firewall rules. It is also available as both agent-based and agentless options.
Protection Modules
Anti-Malware
Integrates with VMware environments for agentless protection, or provides an agent to defend physical servers and virtual desktops in local mode.
Integrates new VMware vShield Endpoint APIs to provide agentless anti-malware protection for VMware virtual machines with zero in-gues footprint. Helps avoid security brown-outs commonly seen in full system scans and pattern updates. Also provides agent-based anti-malware to protect physical servers, Hyper-V and Xen-based virtual servers, public cloud servers as well as virtual desktops in local mode. Coordinates protection with both agentless and agent-based form factors to provide adaptive security to defend virtual servers as they move between the data center and public cloud.
Web Reputation
Strengthens protection against web threats for servers and virtual desktops.
Integrates with the Trend Micro Smart Protection Network web reputation capabilities to safeguard users and applications by blocking access to malicious urls. Provides same capability in virtual environments in agentless mode through the same virtual appliance that also delivers agentless security technologies for greater security without added footprint.
Integrity Monitoring
Detects and reports malicious and unexpected changes to files and systems registry in real time. Now available in agentless form factor.
Provides administrators with the ability to track both authorized and unauthorized changes made to the instance. The ability to detect unauthorized changes is a critical component in your cloud security strategy as it provides the visibility into changes that could indicate the compromise of an instance.
Intrusion Prevention
Shields known vulnerabilities from unlimited exploits until they can be patched.Helps achieve timely protection against known and zero-day attacks. Uses vulnerability rules to shield a known vulnerability — for example those disclosed monthly by Microsoft — from an unlimited number of exploits. Offers out-of-the-box vulnerability protection for over 100 applications, including database, web, email and FTP servers. Automatically delivers rules that shield newly discovered vulnerabilities within hours, and can be pushed out to thousands of servers in minutes, without a system reboot.
Defends against web application vulnerabilities.
Enables compliance with PCI Requirement 6.6 for the protection of web applications and the data that they process. Defends against SQL injections attacks, cross-site scripting attacks, and other web application vulnerabilities. Shields vulnerabilities until code fixes can be completed.
In this Trend Micro Deep Security 9.5 series, we can see the below topics with detailed information which I learned in my experience .
Part -1 – DSM
Part -2 – Relay Server
Part 3 – vShield Endpoint
Part 4 – Filter Driver Installation
Part 5 – Deep Security Virtual Appliance – DSVA
Part 6 – Deep Security Agent
Part 7 – Smart Scanning Protection Server – SSP Server
Part 8 – Policies and Exclusions
Part 9 – Vmtools with vShield driver installation.
Part 10 – Events and Monitoring
Part 11 – VDI Environment – Agent Protection
Part 12 – VDI Environment – Agentless Protection
Part 13 – SP 1 and Relay Server Upgrade
Part 14 – Filter Driver and DSVA Upgrade
Part 15 – NSX Agentless Protection.
Update:2\27\2016
Also check the new blog about Trend Micro Deep Security Manager 9.6 Upgrade ( 9.5 SP1 – 9.6 ) and Trend DSM 9.6 SP1 windows support and steps to install the filter driver \ DSVA on ESX5.x under Trend DSM 6.0 SP1
Part -1 – Deep Security Manager –
Hardware Requirement :
- Memory 8GB , which includes : 4GB heap memory and 1.5 GB JVM and 2 GB OS overhead.
- Disk Space : 2GB ( 5 GB recommended )
- OS – Windows Server 2012\2008 R2 ( 64 bit recommended )
- DB – Oracle 11g, Oracle 11g Express, Microsoft SQL Server 2012 \2008
- Memory : 4 GB – By Default MAX Memory Usage.
- Disk Space : 75GB (150 GB recommended )
Software Requirement :
VMware vSphere (ESXi) 5.0\5.1\5.5
VMware vCenter 5.0\5.1\5.5
VMware vShield Manager 5.1\5.5.3
Trend Micro Deep Security Manager (DSM) 9.5
Trend Micro Deep Security Relay Agent
Trend Micro Deep Security (DS) Filter Driver
Trend Micro Deep Security Virtual Appliance (DSVA)
Trend Micro Smart Protection Server ( SPS )
Trend Micro Deep Security Notifier
Trend Micro Deep Security Manager (DSM) 9.5 :
Centralized web-based management console for controlling and managing all Deep Security enforcement components like Deep Security Agent DSA’s and Deep Security virtual Appliance DSVA’s . As per the Trend it is recommended to be windows 2008/2012 R2 64bit virtual server.
The Deep Security Manager coordinates the protection being provided to each guest virtual machine. This is done through the Deep Security Virtual Appliance which uses the VMware Endpoint API to apply the protection to the virtual machines. The Deep Security Filter driver controls network traffic in and out of the guest virtual machines.
Deployment of DSM ( Deep Security Manager )
We need to use the FQDN and it should be resolvable by all the other components.
Its recommended to have at least one secondary DSM node for redundancy and not more than 3 nodes. Also make sure all nodes and the DB must be in the same network segment.
3. Make sure below ports are opened before proceeding the Installation
4. Port Usage:
5. Pls find the communication details of the DSM and its Purpose and make sure all the communication is working fine before planning the installation.
Screen shots are taken from the Trend doc.
Connect the DB using the ODBC connection on the DSM Server to check the connectivity between the DB and the DSM.
ODBC is not required but it will help for troubleshooting the DB connectivity issue and after the installation we can get the DB information from the below file path.Just additional info…
DSM Installation Steps..
Download the DSM from the Trend Download link and click the Installation EXE.
Click Next.
Provide the DB Instance IP and Connect the DB.
Provide the License details.
Give the FQDN of DSM .
Set the password for the DSM , Default Username is MasterAdmin.
It will start with all the packages installation in it .
The Deep Security Manager (DSM) JVM default setting for maximum memory usage is 4GB and based on our environment requirement below we need to plan on memory.
Below PIC and Memory info was taken from the Trend Doc.
In case if our DSM Server has more memory and the agent count also like mentioned in the above PIC then we can modify the default JVM Memory .
Default settings can be verified under System > System Information and in the System Details area, expand Manager Node >
To configure the amount of memory available to the Deep Security Manager: For Windows:
1. Go to the Deep Security Manager directory (the same directory as Deep Security Manager.exe). e.g. C:\Program Files\Trend Micro\Deep Security Manager.
2. Create a new file called Deep Security Manager.vmoptions.
3. Edit the file by adding the line: -Xmx8g (in this example, “8g” will make 8 GB memory available to the DSM.)
4. Save the file and restart DSM.
For Linux: 1. Go to the Deep Security Manager directory (/opt/dsm)
2. Create a new file called dsm_s.vmoptions.
3. Edit the file by adding the line: -Xmx8g (in this example, “8g” will make 8 GB memory available to the DSM.)
4. Save the file and restart DSM.
You can verify the new setting by going to System > System Information and in the System Details area, expand Manager Node > Memory. The Maximum Memory value should now indicate the new configuration setting.
Once the Installation is completed then we need to add the AD, VC and vSheild to the DSM.
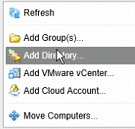
Go to the Computers and right click to select the Add Directory.
Once AD is added , Next step is to add the VC.
Once VC is connected , It will ask to add the vSheild Manager.
Give next and finish the configuration part , Now we can see all the AD Computer Objects and the VC in the DSM.
Adding AD users and Groups in Trend DSM.
Go to Administration-User Managment – Synchronize with Directory and Provide the below AD Server information. By using the query (&(objectClass=user)(| (cn=User1 *)(cn=User2*)(cn=User3*))) we can import the individual users and for the group use the query (cn=*Group_Name*) , Once its imported then we can add to the appropriate roles.
Pls check my next blog for the Relay-Server configuration and its function.
Reference :
http://esupport.trendmicro.com/solution/en-US/1060007.aspx
Deep Security 9.5 Administrator’s Guide Product Features 10


































Pingback: Trend Micro Deep Security 9.5 -Part 2 | Techbrainblog
Pingback: Trend Micro Deep Security 9.5 ( vShield Endpoint ) – Part 3 | Techbrainblog
Pingback: Trend Micro Deep Security 9.5 ( Filter Driver Installation ) – Part 4 | Techbrainblog
Pingback: Trend Micro Deep Security 9.5 ( Deep Security Virtual Appliance-DSVA) – Part 4 | Techbrainblog
Pingback: Trend Micro Deep Security 9.5 ( Deep Security Agent ) – Part 6 | Techbrainblog
Pingback: Trend Micro Deep Security 9.5 ( Smart Scanning Protection Server – SSP Server) – Part 7 | Techbrainblog
Thank you for your post, I think it will be very useful to me.
LikeLike
Thanks…Once i get time , will update more blogs on Trend DSM ( VMtools , VDI NSX )…Pls follow me or check for the updates in coming weeks…
LikeLike
Aw, this was an incredibly nice post. Taking the time and actual effort to proxuce a superb article…
but what can I say… I put things off a whole lot and don’t manage to get nearly anything done.
LikeLiked by 1 person
I’d like to find out more? I’d like to find out more details.
LikeLike
Pingback: Trend Micro Deep Security Manager 9.6 windows 10 support – part 2 | Techbrainblog
Pingback: Trend Micro Deep Security Manager 9.6 – Installing the filter driver on ESX5.1 – Part 3 | Techbrainblog
Pingback: Manually updating the Deep Security Manager (DSM) database before upgrading to 9.6 SP1 – Part -4 | Techbrainblog
Pingback: Trend Micro Deep Security Manager 9.6 ( service pack 1 upgrade ) – Part 5 | Techbrainblog
Pingback: Trend Micro Deep Security ( Event Based Tasks to activate the VM moved | Techbrainblog
Pingback: Trend Deep security Protection on AWS – Part 1 | Techbrainblog