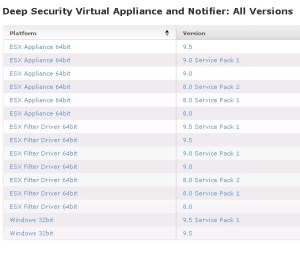
Pls check my previous blogs for the DSM , Relay Server , vShield End Point , Filter Driver,DSVA, DSA , SSP Server , Policies and Exclusions , Events and Monitoring , VMtools and VDI Environment with Agent Protection and Agentless Protection ,Trend DPM Service Pack and Relay Server Upgrdae and Trend Filter Driver and Deep Security Virtual Appliance .In this blog we can see the Agentless protection in an NSX-V Environment.
Before going in to the topic, pls check my other blogs also on the implementation of the NSX Manager 6.1.4 so that you can get more information on the same.
First add the vCenter to the DSM and when it prompt for the vShield or NSX Manager , provide the NSX Manager details.

Preparing ESXi Servers
Before the Deep Security Virtual Appliance service can be deployed to your datacenter, your ESXi servers must first be prepared by installing the drivers necessary for network traffic inspection. This operation is performed on the cluster.Pls check my blog preparing the cluster and host for more info.
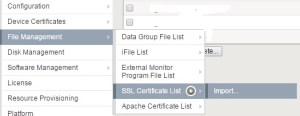
Login to the web client Home – Networking and Security – Installation – Click Host preparation.

Pls check my blog for more details on the installation steps.
Installing the Guest Introspection Service.
Once the Host Preparation is done then the next step is to install the Guest Introspection Service.
To protect the VMs with Deep Security , We have to install the Guest Introspection Service on the cluster that contains the ESXi Servers.
Go to Home – Networking & Security – Installation – Service Deployment and click +
Select Service & Schedule – Select Guest Introspection:

Select the Cluster

Choose the Storage and Network

Click Finish.

Creating the NSX Security Groups:
VM must be organized into a NSX Security Group before a vSphere policy is assigned to them.
Go to the Security Groups – Home – Networking & Security – Service Composer and click the New Security Group icon.
Give the name to the security Group.

Define Dynamic Membership: If you wish to restrict membership in this group based on certain filtering criteria, enter those criteria here

There are many ways to include or exclude objects in a NSX Security Group, but for this example, we will simply include the NSX cluster that contains the hosts and VMs that we want to protect. In the Select objects to include options, select Cluster from the Object Type menu, and move the NSX Cluster that contains the VMs to protect to the Selected Objects column.


Click Finish to create the new security group.
Install the Deep Security Service.
To provide agentless protection to the virtual machines on your ESXi servers, you must install the Deep Security service (the Deep Security Virtual Appliance) on your ESXi servers
Login to the web-client Home – Networking and Security – Installation – Service Deployments and click +

Select Services & Schedule : Select the Trend Micro Deep Security service:

Select the cluster

Select Storage and Network:

Click Next and Finish to complete.
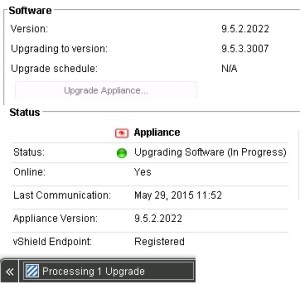
Once the deployment is completed , we will see the Deep Security Service in the list of Network & Security Service Deployment.

Create an NSX Security Policy:
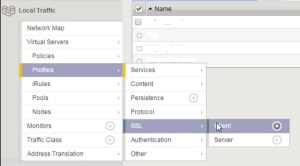
Now we have to create the NSX Security Policy with Deep Security enabled as both an Endpoint Service and as a Network Introspection Service.
Go to Home – Networking and Security – Service Composer and Click on the Security Policies – Click New Security Policy.
Name and Description: give a name to the new policy:

Guest Introspection Services : Click add to add an Enpoint Service and provide the name for the Endpoint Service.

Click Next and in Firewall Rules do make any changes .
Network Introspection Service :
We need to add two Network Introspection Services to the Network Security Policy : Outbound \Inbound Traffic.



Once done click finish and now we have created the NSX Security Policy for Deep Security.
Apply the NSX Security Policy to the NSX Security Group
Go to Home – Networking & Security – Service Composer – select the newly created policy and click Apply the Security Policy icon.

The NSX Security Policy is now applied to the VMs in the NSX Security Group.
Adding Additional ESXi Servers to Your NSX Cluster After Deep Security Integration
Adding a new ESXi server to a NSX cluster that is protected by Deep Security must be done in the following sequence:
1. Add Host to the DataCenter but not directly to the cluster.
2. Connect the Host to the Distributed Switch.
3. Move the Host into the cluster. Once the Host is moved into the cluster, the Deep Security service will be deployed automatically.
Apply Deep Security Protection to Your VMs
Apply the Policy and also install the vShield Driver on the VMs and activate the same , Pls see my previous blogs on the same.

Tested the web url and also with Test Virus , result is below..