This blog is about configuring the vCenter SSO LB using the Microsoft Load-Balancing Manager , I have noticed that lot of blog and KB mentioning about the configuration of the LB using F5 , Citrix NetScalar and VMware Edge but not using the Microsoft LB which is very easy and no need any external requirements like addtional Load Balancer or any Appliance . Anyhow as per the VMware they wont support for any third-party product so going with Microsoft LB doesn’t make any difference.
I have followed the VMware document in this blog for configuring the SSO LB Setup.
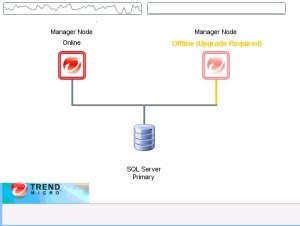
VMware recommends the centralized SSO server when we have 8 or more vCenter server are present in our location.

PIC is taken from the VMware.
Pre-installation Checklist::
- We need two VMs for the SSO LB with the Load Balancer IP.

- Download the latest vCenter Server ISO for the SSO installation.
- Need Microsoft Visual C++ 2008 Redistributable Package.Pls note we need 32-bit because OpenSSL tool has a dependency on the same.
- Download and install Win32 OpenSSL (version 0.9.8)
- Create the Certificate Folder Structure . C:\Certs\SSO
- Create a vCenter Single Sign-On Configuration file. C:\certs\sso\sso.cfg
[ req ]
default_bits = 2048
default_keyfile = rui.key
distinguished_name = req_distinguished_name
encrypt_key = no
prompt = no
string_mask = nombstr
req_extensions = v3_req
[ v3_req ]
basicConstraints = CA:FALSE
keyUsage = digitalSignature, keyEncipherment, dataEncipherment
extendedKeyUsage = serverAuth, clientAuth
subjectAltName = DNS:sso1, DNS:sso1.vmware.local, DNS:sso2, DNS:sso2.vmware.local,
DNS:sso.vmware.local, IP:192.168.110.40
[ req_distinguished_name ]
countryName = Country
stateOrProvinceName = State
localityName = City
0.organizationName = Company Name
organizationalUnitName = vCenterSSO
commonName = sso.vmware.local
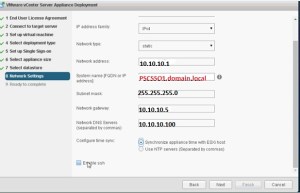
Depoly the first vCenter Single Sign-on Installation.
Login to the VMware.Local
On the Menu choose the vCenter Single Sign-on option under Custom Install and click Install
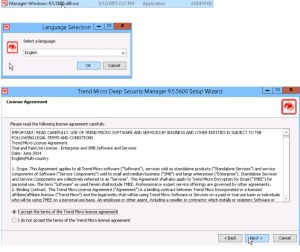
Give Next in the Wizard and accept the Agreement
Select the First vCenter Server below option.

Provide the Password for the built-in administrator@vsphere.local

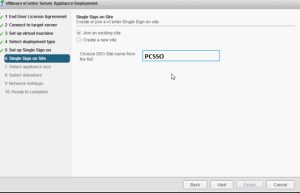
Select the Site name – Select the SSO Port Settings – Finish the Installation.
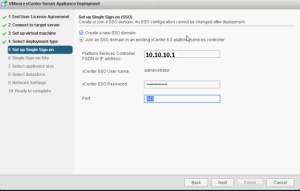
Additional vCenter single Sign-On Installations
Connect to the vCenter Server ISO on the second server sso2.vmware.local.
On the Menu choose the vCenter Single Sign-on option under Custom Install and click Install
Give Next in the Wizard and accept the Agreement

Provide the Partner host name as sso1.vmware.local and provide the password for the built-in administrator@vsphere.local account used with sso1.vmware.local and click Next.
Accept the host certificate and give Next and Complete the Installation.
vCenter Single Sign-On Certificates .
All vCenter Single Sign-On servers that participate in the loadbalanced configuration require certificate updates. In our example, we will use a Microsoft certificate authority (CA) as our trusted root authority and will generate certificate requests with OpenSSL.
Generate the Certificate Request.
Open the CMD Prompt with Administrator Rights and run the below command to create the certificate request and export the private key.
openssl req -new -nodes -out c:\certs\sso\rui.csr –keyout c:\certs\sso\rui-orig.key -config c:\certs\sso\sso.cfg.

Run the Following to convert the key into RSA Format:
openssl rsa -in c:\certs\sso\rui-orig.key -out c:\certs\sso\rui.key

Download the CAs Root Certificate with Based64 encoding. Rename it to certnew.cer – Root64.cer and save it to the c:\certs

With a text editor, open the private key C:\certs\sso\rui.csr and copy the entire contents into the CA certificate request field. Select the template with data encipherment enabled (optional step previously mentioned) and download the certificate as Base64 encoded. In our example, the file generated is named certnew.cer and is renamed as rui.crt and then placed into the following: C:\certs\sso



Run the following to create an archive file (ssoserver.p12) of all certificates and keys: openssl pkcs12 –export –in c:\certs\sso\rui.crt –inkey c:\certs\sso\rui.key – certfile c:\certs\Root64.cer –name “ssoserver” –passout pass:changeme –out c:\certs\ sso\ssoserver.p12

Change to the VMware directory by typing the following: CD C:\Program Files\Common Files\VMware\VMware vCenter Server – Java Components\bin\
Run the following to create the Java KeyStore:
keytool –v –importkeystore –srckeystore C:\certs\sso\ssoserver.p12 –srcstoretype pkcs12 –srcstorepass changeme –srcalias ssoserver –destkeystore C:\certs\sso\roottrust.jks -deststoretype JKS –deststorepass testpassword –destkeypass testpassword
If asked whether the existing entry alias ssoserver exists, overwrite? Type: yes
Run the following to add the root certificate to the Java KeyStore:
keytool –v –importcert –keystore C:\certs\sso\root-trust.jks –deststoretype JKS – storepass testpassword –keypass testpassword –file C:\certs\Root64.cer –alias root-ca
When asked whether to trust this certificate, type: yes

Run the following to copy the Java KeyStore to the required Java KeyStore name:
Copy C:\certs\sso\root-trust.jks C:\certs\sso\server-identity.jk

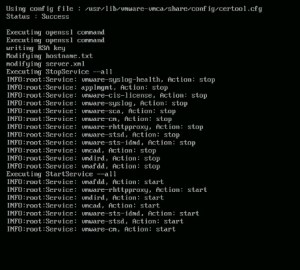
Configuring CA-Signed SSL Certificates
Run the following to set the correct environment variables:
SET JAVA_HOME=C:\Program Files\Common Files\VMware\VMware vCenter Server – Java Components SET PATH=%PATH%;C:\Program Files\VMware\Infrastructure\VMware\CIS\vmware-sso;%JAVA_ HOME%\bin

Change to the OpenSSL directory; type and run the following: CD \OpenSSL\bin
Register the new root certificate in the VMware trust store; type and run the following:
openssl x509 –noout –subject_hash –in C:\certs\Root64.cer
This will create an eight-digit hexadecimal value that will be used below.
Run the following to create an SSL directory:
mkdir c:\ProgramData\VMware\SSL
Run the following to copy the Root64.cer certificate to the SSL folder:
Copy C:\certs\Root64.cer C:\ProgramData\VMware\SSL\.0
Run the following to copy the Root64.cer file to the SSL folder and rename it to ca_certificates.crt:
more C:\certs\Root64.cer >> C:\ProgramData\VMware\SSL\ca_certificates.crt

To change the vCenter Single Sign-On server configuration to reflect the NLB, with a text editor, create three text files within the C:\certs directory and name as shown.
Filename: C:\certs\admin.properties
[service]
friendlyName=The administrative interface of the SSO server
version=1.5
ownerId=
productId=product:sso
type=urn:sso:admin
description=The administrative interface of the SSO server
[endpoint0]
uri=https://sso.vmware.local:7444/sso-adminserver/sdk/vsphere.local
ssl=c:\certs\Root64.cer
protocol=vmomi
Filename: C:\certs\gc.properties
[service]
friendlyName=The group check interface of the SSO server
version=1.5
ownerId=
productId=product:sso
type=urn:sso:groupcheck
description=The group check interface of the SSO server
[endpoint0]
uri=https://sso.vmware.local:7444/sso-adminserver/sdk/vsphere.local
ssl=c:\certs\Root64.cer
protocol=vmomi
Filename: C:\certs\sts.properties
[service]
friendlyName=STS for Single Sign On
version=1.5
ownerId=
productId=product:sso
type=urn:sso:sts
description=The Security Token Service of the Single Sign On server.
[endpoint0]
uri=https://sso.vmware.local:7444/ims/STSService/vsphere.local
ssl=c:\certs\Root64.cer
protocol=wsTrust
Run the following to list the vCenter Single Sign-On services: ssolscli listServices https://sso1.vmware.local:7444/lookupservice/sdk

PIC is taken from the VMware.
For each service returned, the first field will display as the following: :
Each service site name and 32-digit hexadecimal value must be saved to a text file for each corresponding service type:
ECHO Palo Alto:<thirty two digit hexadecimal value> >> C:\certs\gc_id
ECHO Palo Alto:<thirty two digit hexadecimal value> >> C:\certs\sts_id
ECHO Palo Alto:<thirty two digit hexadecimal value> >> C:\certs\admin_id
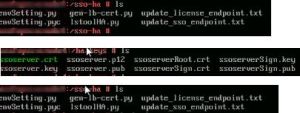
Open a Windows Explorer window and navigate to the following: C:\ProgramData\VMware\CIS\runtime\VMwareSTS\conf) Create a backup directory and make a backup of the following files by copying them into the backup folder:
ssoserver.crt
ssoserver.key
ssoserver.p12
In the command prompt windows, copy the three certificate files to the correct destination by typing the following:
copy C:\certs\sso\ssoserver.p12 c:\ProgramData\VMware\CIS\runtime\VMwareSTS\conf\ ssoserver.p12 copy
C:\certs\Root64.cer c:\ProgramData\VMware\CIS\runtime\VMwareSTS\conf\ ssoserver.crt copy
C:\certs\sso\rui.key c:\ProgramData\VMware\CIS\runtime\VMwareSTS\conf\ ssoserver.key
Before we can update the vCenter Single Sign-On service information, we must add the sso.vmware.local into the local host files, because this entry will create an error prior to configuration of the load balancer.
Type the following: notepad C:\Windows\System32\Drivers\etc\hosts Then add the following:
192.168.110.41 sso.vmware.local #Node1 IP
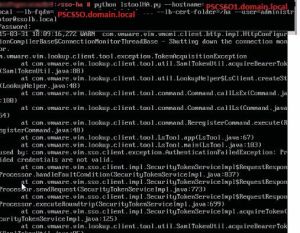
Pls note if we are not adding the entry then we will receive the below error when we running the ssolsclt to update the service.

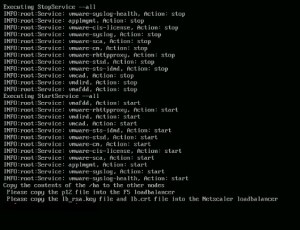
Run the following to update the three vCenter Single Sign-On services with the service files created with
the NLB configuration. Type the following:
ssolscli updateService -d https://sso1.vmware.local:7444/lookupservice/sdk -u administrator@vsphere.local -p <password> -si C:\certs\gc_id –ip C:\certs\gc.properties
ssolscli updateService -d https://sso1.vmware.local:7444/lookupservice/sdk -u administrator@vsphere.local -p <password> -si C:\certs\admin_id –ip C:\certs\admin.properties
ssolscli updateService -d https://sso1.vmware.local:7444/lookupservice/sdk -u administrator@vsphere.local -p <password> -si C:\certs\sts_id –ip C:\certs\sts.properties
NOTE: If you receive a Server certificate assertion not verified and thumbprint not matched error, follow step
Restart the VMware Security Token Service and repeat the command.
net stop VMwareSTS \ net start VMwareSTS
Confirm that the updates have been applied by listing the vCenter Single Sign-On services.
Type the following:
ssolscli listServices https://sso1.vmware.local:7444/lookupservice/sdk
The endpoints entry should now show the load balance URL sso.vmware.local for each service.
Remove the temporary host entry applied to the local hosts file by deleting the sso.vmware.local entry.
Log in to sso2.vmware.local and open an elevated command prompt.
Open a Windows Explorer window. Navigate to \\sso1.vmware.local\c$ and copy the certs directory to C:\ on sso2.vmware.local \\sso1.vmware.local\c$\ProgramData\VMware and copy the SSL directory to C:\ProgramData\VMware on sso2.vmware.local
Run the following to set the correct environment variables:
SET JAVA_HOME=C:\Program Files\Common Files\VMware\VMware vCenter Server – Java Components SET PATH=%PATH%;C:\Program Files\VMware\Infrastructure\VMware\CIS\vmware-sso;%JAVA_ HOME%\bin
Before we can update the vCenter Single Sign-On service information, we must add the sso.vmware. local into the local host’s files on sso2.vmware.local because this entry will create an error prior to configuration of the load balancer. Type notepad C:\Windows\System32\Drivers\etc\hosts and add
192.168.110.42 sso.vmware.local #Node 2 IP
In the command prompt window, copy the three update files to the correct destination. Type the following:
copy C:\certs\sso\ssoserver.p12 c:\ProgramData\VMware\CIS\runtime\VMwareSTS\conf\ ssoserver.p12
copy C:\certs\Root64.cer c:\ProgramData\VMware\CIS\runtime\VMwareSTS\conf\ ssoserver.crt
copy C:\certs\sso\rui.key c:\ProgramData\VMware\CIS\runtime\VMwareSTS\conf\ ssoserver.key
Restart the VMware Security Token Service to accept the updated certificate files. Type the following: net stop VMwareSTS
net start VMwareSTS
Update the three services with the current information. Type the following:
ssolscli updateService -d https://sso2.vmware.local:7444/lookupservice/sdk -u administrator@vsphere.local -p -si C:\certs\gc_id –ip C:\certs\ gc.properties
ssolscli updateService -d https://sso2.vmware.local:7444/lookupservice/sdk -u administrator@vsphere.local -p -si C:\certs\admin_id –ip C:\certs\admin.Properties
ssolscli updateService -d https://sso2.vmware.local:7444/lookupservice/sdk -u administrator@vsphere.local -p -si C:\certs\sts_id –ip C:\certs\sts. Properties
Confirm by typing the following that the updates have been applied on the both the nodes.
ssolscli listServices https://sso1.vmware.local:7444/lookupservice/sdk

ssolscli listServices https://sso2.vmware.local:7444/lookupservice/sdk

The endpoints entry (line 4) should now show the load balance URL sso.vmware.local for each service. Remove the temporary host entry applied to the local host’s file by deleting the sso.vmware.local entry.
Next comes the Configuring the Microsoft Network Load Balancer.
Hardware requirements
To run an NLB cluster, the following are hardware requirements:
All hosts in the cluster must reside on the same subnet.
There is no restriction on the number of network adapters on each host, and different hosts can have a different number of adapters.
Within each cluster, all network adapters must be either multicast or unicast. NLB does not support a mixed environment of multicast and unicast within a single cluster.
If you use the unicast mode, the network adapter that is used to handle client-to-cluster traffic must support changing its media access control (MAC) address.
Software requirements
To run an NLB cluster, the following are software requirements:
Only TCP/IP can be used on the adapter for which NLB is enabled on each host. Do not add any other protocols (for example, IPX) to this adapter.
The IP addresses of the servers in the cluster must be static.
Install the Network Load Balancer Feature on both the nodes.


Add the second NIC on both the nodes and assign the Static IP with the same subnet of the load balancer IP.
LB : 192.168.110.40
Node 1 Second NIC IP : 192.168.110.43
Node 2 Second NIC IP : 192.168.110.44
Open the Network Load Blancing Manager form the administrative tools on Node1.
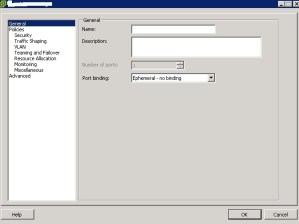
Create the New Cluster.

Connect the Node 1 and select the second NIC IP.

Select Next Host Parameters

Priority Unique Host Identifier should be 1 for the top and 32 for the least priority and we should not have the same number on other nodes in the cluster.
Initial Host State – It is for to mention when can be the host to re-join in to the cluster after reboot , keep it as default Started .
Next Add the Load Balancer IP.



Provide the Load Balancer FQDN Name.
Select the Multicast which is used to communicate between two nodes.

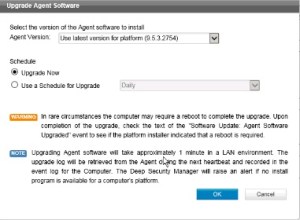
Port rule : Delete the default and change the port to 7444 and select the Affinity to None so that traffic will be routed to the both the nodes and in case if we select Single and it will send the traffic only to single node.

Select Add host cluster and connect the Second Load Balancer.



Note here the priority it is 2 .


Once everything is configured then we can see the Cluster with the LB having two nodes and test the configuration by power down the one node and try the https://sso.vmware.com:7444/lookupservice/sdk link.Do the same test on the second node.
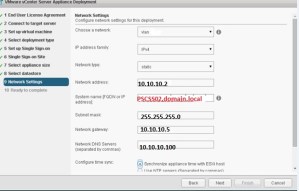
Provide the LB details while configuring the vCenter , Inventory Service and Webclient .


We can find the SSOLB name with details by login in to the web client.

Power down the SSO Node 1 and test the connectivity of the VC by having only the SSO Node 2 and do the same testing for the Node 2 also.
Reference :
Click to access VMware_vCenter_Server_5.5_LB_SSO_Technical_Reference.pdf
https://www.google.com/webhp?sourceid=chrome-instant&ion=1&espv=2&ie=UTF-8#q=microsoft+network+load+balancing+2012